 What is identity and access management?
What is identity and access management?
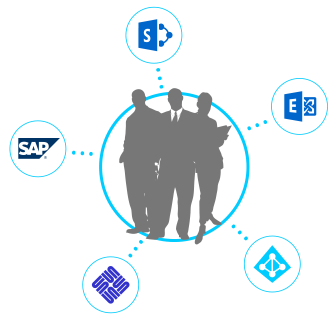
An organization or business may have a number of systems in use such as Active Directory, Exchange, Oracle and SharePoint, and they may have hundreds or even thousands of users who need to access them. Managing all of these users’ accounts and the access allowed for each one is generally known as identity and access management, or IAM.
Without a proper identity and access management solution, user access controls and login credentials need to be created manually for each user on each individual system. This approach is tedious and prone to issues involving delays, operator errors and security holes, not to mention paperwork. Unfortunately, this is the traditional approach that many businesses still use today.
As the business and number of users grow, trying to manage and govern them all becomes a mounting concern that cannot be ignored. The main problem to be faced is that traditional IAM solutions take a huge investment in both time and money just to get them set up, often taking 6 months or more just to get it working, let alone up to speed.
How IDM365 solves the problems of IAM
IDM365 is a unique identity and access management solution that is designed to make managing systems and governing users simple and cost-effective. To do this, automated tools are used to clean up and organize existing users and roles before taking over the tasks needed for provisioning. This approach greatly speeds up the implementation process. IDM365’s user-friendly interface then allows precise access to be requested and granted to every user based on their position and roles. With robust workflow managing and tracking, reports can be generated on the fly with any type of information you could imagine about things like user identities, access permissions, connected systems and any actions taken through the interface.
IDM365 connects to various systems through standard and individual APIs. With direct access to each system in the infrastructure, IDM365 is able to manage system identities and govern access across the infrastructure from a central Single Point of Truth (SPoT). At the same time, IDM365 does not replace existing systems. Rather, it provides an extra layer that unifies account creation, identity management and access governance in a more organized and efficient way.
If necessary, each system can still be accessed directly, so there is no fear of IDM365 shutting down the system. What IDM365 does is make running those systems much smoother.
The article What is IDM365? explains some of these concepts in more detail.
What is the IDM365 attribute store?
As its name suggests, IDM365’s attribute store stores the different attributes for indentities that have been configured through IDM365.
Each business has their own requirements that may require different types of attributes for each of their users. One business may provide workers with a ‘salary number’ that they want stored or reflected in AD somehow, perhaps for backup purposes. Another business might use ticket numbers and require additional details for contract workers, and a third might have a virtual department set up for robots and machine workers that require a spec sheet. The concept of the attribute store is to generalize these rules so that the attributes needed can be specified for each group of identities from a single interface.
Through the IDM365 interface, attribute store managers are able to specify the exact attributes that are required for users depending on the attributes they already have. The attribute store will then be referenced when setting up new identities, only asking for those attributes that have been set up for whatever divisions have been selected. For example, users in a specific business unit, department, location or other type of division may require certain contact information, and users with temporary employment may require stored information regarding the work they have been assigned. The attributes required for each identity will be reflected in the fields that are shown in the interface.
When configuring what attributes should be requested, the attribute store manager can select the type of field and data that is needed. For example, the user’s gender could be set up as a multiple choice option, their date of birth as a date entry, a signature line as a free-text area, and a scanned employment agreement as a file upload. As mentioned before, every business, enterprize, organization, office, workplace and otherwise is different; the attribute store is 100% configurable to accomodate those differences.
Features
- Management-friendly configuration of required attributes from the same IDM365 interface used for identity and access management
- Custom attibutes per client that can be synchonized to systems based on logic and business rules
- Configurable data types for requested attributes
IDM365 and MIM
MIM stands for Microsoft Identity Manager, and is new for 2015. You can read about the initial release on the Active Directory Team Blog. In past years, Microsoft has offered an identity manager (FIM) as part of their largely deprecated Forefront offering. MIM is a modernized offering based on FIM that Microsoft is now making available as part of their Azure Active Directory Premium offering. The focus of MIM is to provide role management, certificate management, group management, password reset options and identity synchronization.
MIM at its core was designed as an identity and access management framework for Azure and Windows Server Active Directory to help control other systems as well. MIM looks at the state of attributes in the source identity store (the value of each attribute and whether it has changed) and synchronizes those attributes with the systems and apps it is connected to. In addition to identities, MIM can be used to enforce corporate security policies across the system infrastructure, thus providing a consistent and secure environment for businesses to work in.
Integration with IDM365
IDM365 uses its own directory store for identities and access permissions that can be read through a secure web API. Through this API, MIM can update the various systems it is set up to control with the attributes stored and managed in IDM365. Configured as a middleman, MIM works in the background to make sure all systems stay synchronized while following any rules and policies that have been defined for it regarding what actions to take.
Instead of an event-based approach where systems are updated based on actions that are performed, MIM uses a monitoring or state-based approach for integration that assumes one side is always right, thereby ensuring consistancy across systems.
Features and Advantages of Using MIM
- Consistancy across systems
- Policy enforcement based on rules and conditions that keeps things up to date
- Easy synchronization of user identities across Windows Server Active Directory, Microsoft Azure Active Directory, remote folders and more
- Enhanced self-service options for users that reduce help desk traffic
- Workflow based certification of users
- Simplified administration of identity life cycles through workflows and business rules
- Improved security and compliance monitoring
- Simplified integration with systems through the large API and web services pool
Getting started
Perhaps you’re wondering if IDM365 would be a good fit for your organization. You might have questions like: “Where do I start? What is the best way to evaluate IDM365 and whether it has what we need? What steps would I need to take before we can get up and running with it?” Would you believe that those answers are easy? Here are a few paths we can suggest:
“I want to go hands-on and try it.”
No problem. Here’s what to do:
- Start by requesting a Live Demo. No account is required, and you can instantly get a feel for the interface by following the tutorial in our limited functionality demo.
- Request a Proof of Concept. We’ll respond with details and discuss with you what’s involved in getting a secure test system with your data so you can play with it. This is very quick to set up and will simulate how IDM365 would work in your environment.
- If you decide that IDM365 is a good fit, the next step is our rapid 4-step implementation process that will get you fully up and running and ready for the future.
“I want all the details up front.”
Great, we will happily provide you with as much information as you want. Here are the resources:
- Explore the website and learn about identity management, user access management, access governance and IDM365. Click on MORE to see a full menu with all the information that is available on the website.
- Download the documents. You will notice under the full menu that there are some links underneath different sections with document icons. These are downloadable PDFs that can provide you with more detailed or technical information, as well as a checklist or two.
- Check out our video tutorials hosted on Vimeo that explain how to do perform various tasks like adding users and approving access requests. These short how-to videos present relevant actions in a simple, straightforward and easy-to-follow manner, and are available directly in the IDM365 interface whenever they may be needed.
- Request more information about specific topics or questions you may have. Many pages have links to request specific pieces of information regarding what is preseted on that page. Some information is not published directly on the site, such as that about our clients or detailed, technical information about our implementation process, but we are happy to provide such information upon request.
- Connect with us on social media like Twitter, LinkedIn and Google+, and subscribe to our blog. Stay in the loop and be the first to know of any new developments.
- At any point during your research, when you feel you’re ready to test some things out or just talk to us about something, go ahead and contact us and we can discuss next steps.
“I want to talk to a real person.”
We would love to talk to you, too! Just give us a call or send us an email with contact information and you’ll get to talk to some very friendly and knowledgeable people who can help you with whatever questions you have. We can also guide you through getting started if that’s what you would like. You’re always welcome to connect with us in any way that you prefer.
We look forward to hearing from you.